Pastenym — A privacy-friendly sharing service
Pastenym allows you to share text simply, anonymously and with privacy. Inspired by pastebin.com, pastenym runs on the Nym mixnet.
This network allows to protect one’s data and metadata from the eyes of governments, ISPs and any other organization/actor that would analyze (=monitor) the network and the communications.
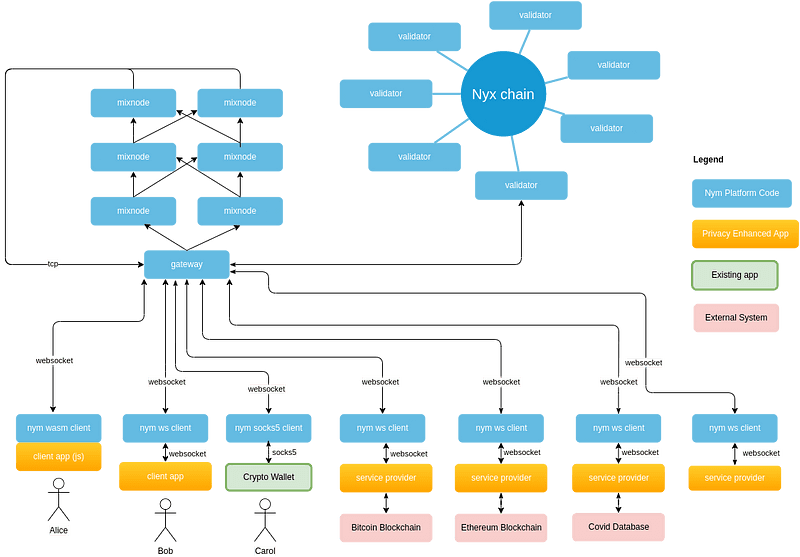
The mixnet allows, thanks to different mechanisms, to protect the identity of people when they communicate on this network (for more details https://nymtech.net/docs/stable/architecture/network-overview#overview).
Mixnet design by Nym
**Pastebin/ Privatebin
**Systems like pastebin.com or privatebin.info (fork of zerobin) allow quick and easy exchange of text. Privatebin adds a layer of encryption that ensures that only the sender and receivers have access to the content.
When using these websites, it is quite possible for an observer to detect actions performed by users, such as retrieving or sharing a text. This information can be correlated with information from other services, such as instant messaging or emailing. This is possible because metadata is not protected on these services.
Pastenym
Pastenym is an adaptation of pastebin.com, using Nym’s mixnet, to protect users and their data but especially their metadata.
To understand the difference, it is important to understand how this service works. At the time of a connection to the Web site, which is only a “frontend”, the navigator will use the client (nym-client) developed by Nym to connect to the mixnet via a gateway and obtain an identity.
The user will then enter the text she wants to share and click on “Send”.
At this moment the nym-client will select 3 mixnodes which will take care of transmitting the data and will encrypt the information thanks to the public keys so that they can correctly relay the data to the next mixnode or gateway.
It is the gateway of the recipient, in the case of pastenym the server which hosts the data which will take care to transmit the message. Finally the nym client of pastenym will decrypt the content and store the information. A message will be sent back with a random identifier that allows to find the shared text.
The operation is very similar to the other services, with the only difference that the text to be shared is transmitted through the mixnet. This is what guarantees anonymity and prevents from knowing which computer (IP address) has shared or accessed a text.

Sharing of a text
In case the network is monitored, the only visible connections would be the one from the browser to the server hosting the web service and the one initiated by the nym-client to a gateway of the mixnet, so it is possible to know the destination of the sent and received packets but without the possibility to know if there is really data and to whom they are sent or received. A more complete article will be published later.
To ensure complete protection, the website must use the HTTPS protocol in case the identifier of the text to be recovered is in the URL.
In the mixnet, all information is encrypted and transmitted using SPHINX packets (used in the lightning network) which makes all data traveling through the network look the same. To prevent an observer from detecting when you are communicating, fake packets are generated to simulate constant traffic. These methods prevent an observer from knowing what type of application is in transit (VoIP, chat, browsing, etc.) and who is communicating with whom across the network, so it is extremely difficult to know which server is hosting the database and to find out who has stored information in it to share text because it is only accessible via the mixnet.
In the event that the website is censored or deleted, it is sufficient to recreate a server and deploy it again in order to restore access to the stored texts.
Demonstration
The website https://pastenym.ch is available to share text and test the application.
And here is an example of a shared text : https://pastenym.ch/#/kzXwH3WY&key=ce325aeac6ad4c9ba5275a6e555e1b95
Warning, the project is still in alpha and cannot be used to share sensitive information. The authors of this project take no responsibility for the information transmitted on this service.
**Future developments
**The code is licensed under GPLv3 and available at this address: https://github.com/notrustverify/pastenym
A command line application will be developed to allow better privacy protection and resilience of the service.
Then a non-exhaustive list of features:
Expiration of texts in time or number of readings
Coconut support for authentication
Support of SURB (Single Use Reply Blocks)
Possibility to delete texts
Syntax highlighting
Tags and categories
Support for public paste (without encryption)
Development of a command line application